Navigating NIST, AESO CIP, and NERC CIP — and how to make assessments actionable.
Executive Summary
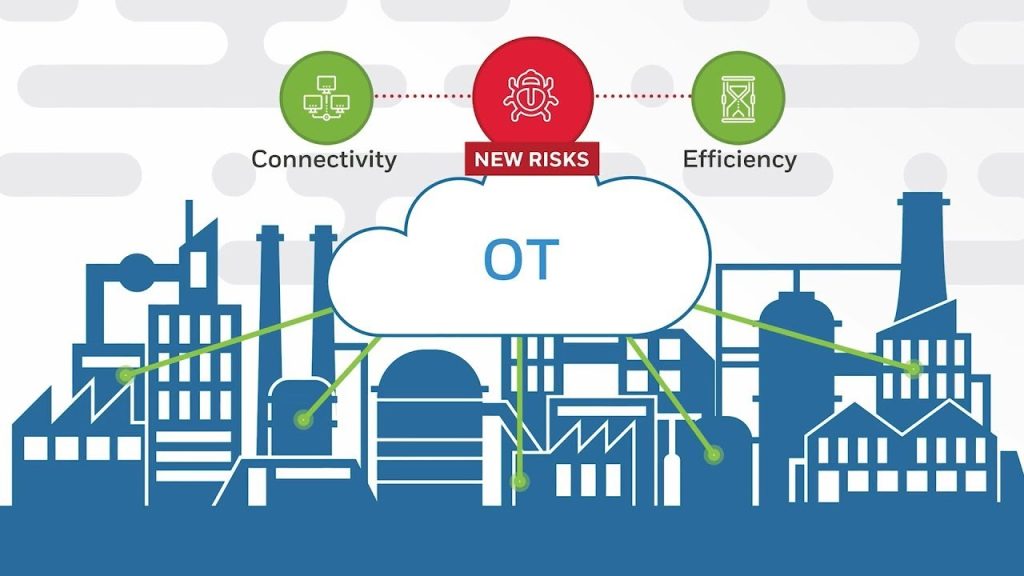
Across Canada, utilities and municipalities are connecting control systems, remote assets, and IoT platforms at unprecedented speed. But greater connectivity means greater exposure. Whether you manage power grids, water treatment, or transportation systems, assessing your Operational Technology (OT) environment against recognized frameworks such as NIST CSF 2.0, NIST SP 800-82r3, AESO CIP, and NERC CIP is no longer optional — it’s essential for resilience, compliance, and public safety.
1. Choosing the Right Framework Mix
NIST CSF 2.0 (2024): Governance and Outcomes
Canada’s municipalities often adopt NIST CSF 2.0 as the umbrella framework because it is flexible and outcome-based. It provides six functions — Govern, Identify, Protect, Detect, Respond, Recover — that translate easily into policy and reporting language for councils or boards.
NIST SP 800-82 Revision 3 (2023): OT-Specific Guidance
While CSF defines what to achieve, NIST 800-82 explains how to secure industrial control systems. It’s the go-to reference for control networks, SCADA, and building automation, with an emphasis on availability, safety, and deterministic operations.
NERC CIP / AESO CIP: Mandatory for the Electric Sector
In provinces such as Alberta, AESO Reliability Standards mirror U.S. NERC CIP requirements. These are mandatory for power entities that could affect the bulk electric system — covering asset categorization, access control, incident response, and supply-chain risk.
CCCS Cross-Sector Readiness Goals (CRGs)
The Canadian Centre for Cyber Security’s 36 CRGs provide a lightweight framework for smaller utilities and municipalities that may not fall under NERC jurisdiction. It’s a bridge between policy intent and technical implementation.
Water and Wastewater
While not regulated under NERC, the AWWA Cybersecurity Guidance Tool has become a practical baseline. It aligns closely with NIST CSF and supports public-works departments in defending critical water operations.
2. The Real-World Assessment Challenges
A. Selecting Controls that Fit OT
Many IT controls — such as automated patching or endpoint agents — can disrupt sensitive process equipment. Assessors must tailor safeguards to industrial constraints by referencing NIST 800-82r3 and IEC 62443-3-3 control objectives.
B. Mapping Frameworks into Industrial Contexts
Use the Purdue Model (ISA-95) to zone assets and apply the right controls at each level. For instance, Level 1/2 devices may require strict allow-listing and physical isolation, while Level 3 systems integrate with enterprise monitoring.
C. Evidence Collection
- Power utilities: follow the CIP Evidence Request Tool (ERT) structure — inventory lists, procedures, training logs, and configuration samples.
- Municipal systems: use NIST CSF Profiles (Current vs Target) to document posture and priorities.
- Capture evidence early; it becomes the backbone of both compliance and funding justification.
D. Reporting and Remediation
Boards and regulators respond better to risk-based roadmaps than raw findings. Tie every recommendation to a measurable risk reduction or operational benefit (e.g., faster recovery, fewer unplanned outages).
For AESO or NERC entities, align mitigation actions to specific CIP requirements; for municipalities, map them to CCCS CRGs or provincial resilience goals.
3. Tools That Accelerate the Process
- NIST CSF 2.0 Reference Tool – Build Current vs Target Profiles.
- CCCS 36 Readiness Goals Toolkit – Canadian prioritization matrix.
- AWWA Cybersecurity Assessment Tool – Water/wastewater-specific checklist.
- MITRE ATT&CK for ICS – Maps adversary behaviors to controls for evidence and SOC use-cases.
- NERC CIP ERT – Template for documentation and audits in the electricity sector.
4. Sector Nuances That Matter
| Sector | Regulatory Pressure | Typical Focus | Primary Challenge |
| Electricity (NERC/AESO) | High – mandatory compliance & audits | Access control, incident response, supply chain | Audit fatigue, documentation depth |
| Water/Wastewater | Moderate – voluntary frameworks | Asset visibility, remote access security | Resource limits, vendor dependencies |
| Transit & Public Infrastructure | Emerging – policy-driven | Network segmentation, monitoring | Multi-vendor integration |
| Municipal IT/OT Convergence | Variable – local bylaw driven | Governance alignment, risk reporting | Talent and ownership clarity |
5. The Grovemex Consulting Approach
At Grovemex, assessments are more than checklists — they’re consulting engagements that build capability.
- Collaborative Scoping: We align engineering, IT, and operations to define what “critical” truly means for your environment.
- Framework Harmonization: We map NIST CSF 2.0, NIST 800-82, and applicable CIP or CCCS CRG controls into a unified, organization-specific model.
- Threat-Informed Analysis: Using MITRE ATT&CK for ICS, we connect technical findings to credible adversary behaviors.
- Evidence & Audit Readiness: For AESO/NERC entities, we prepare artifacts in ERT format; for municipalities, we produce concise CSF dashboards and risk registers.
- Actionable Roadmaps: We deliver a prioritized improvement plan with 30-, 90-, and 180-day milestones tied to business outcomes.
- Capability Transfer: Every engagement includes coaching and knowledge transfer so internal teams can sustain improvements.
6. Why This Matters Now
The Cyber Centre’s 2025 advisories highlight increasing activity from state-aligned groups targeting industrial networks. Combined with aging infrastructure and limited budgets, Canadian public entities face a perfect storm.
Yet the solution isn’t panic — it’s structure, measurement, and steady improvement.
Assessments done right create confidence. They let executives justify investment, regulators verify diligence, and operators trust that safety and cybersecurity can coexist.
Ready to Begin? Consult Grovemex.
Whether you operate a power utility, a water treatment plant, or an integrated municipal network, a well-executed assessment is the first step toward lasting resilience.
Grovemex helps Canadian organizations:
- Conduct standards-aligned OT security assessments (NIST CSF 2.0, NIST 800-82, AESO CIP, NERC CIP).
- Build a governance-based roadmap for continuous improvement.
- Translate findings into fundable, measurable projects that strengthen operations without disrupting them.
�� info@grovemex.com | �� www.grovemex.com
Start your assessment with Grovemex today — and turn compliance into confidence.


